Key points about ingress timeout stream id
Welcome ingress timeout stream id to our blog post on Ingress Timeout Stream ID! In this digital age, network security has become a top priority for organizations worldwide. With the ever-increasing threats and vulnerabilities, it is crucial to have robust measures in place to safeguard sensitive data and prevent unauthorized access.
One such measure that plays a vital role in ensuring network security is Ingress Timeout Stream ID. This powerful tool helps monitor and control incoming traffic, allowing only legitimate connections while blocking potential threats. But what exactly is this technology? How does it work? And how can you optimize its performance?
In this article, we will delve into the world of Ingress Timeout Stream ID, exploring its significance in network security and providing valuable tips for maximizing its effectiveness. So let’s dive right in and unravel the key points about this essential component of secure networking!
What is Ingress Timeout Stream ID?
Ingress Timeout Stream ID, also known as ITSID, is a feature that helps regulate network traffic and enhance security measures. It acts as a filter for incoming connections, allowing only authorized streams to pass through while blocking malicious or unauthorized ones.
At its core, Ingress Timeout Stream ID works by assigning unique identifiers to each network connection. These identifiers are then used to track the duration of each stream and determine whether it should be allowed or terminated based on predefined timeout thresholds.
By implementing Ingress Timeout Stream ID, organizations can effectively control the lifespan of incoming connections. This ensures that resources are not tied up unnecessarily and prevents potential security breaches caused by prolonged exposure to external networks.
Not only does this tool provide an added layer of protection against malicious attacks such as DDoS (Distributed Denial-of-Service), but it also helps optimize network performance by efficiently managing available resources. By terminating idle or suspicious streams promptly, system administrators can allocate bandwidth more effectively and maintain optimal speeds for legitimate connections.
Ingress Timeout Stream ID plays a crucial role in safeguarding network infrastructure from various threats while improving overall efficiency. Its ability to regulate traffic flow and terminate potentially harmful connections makes it an indispensable tool in modern-day network security strategies. Stay tuned as we explore further aspects of this essential technology!
Why is it important for network security?
Network security is a critical concern in today’s digital landscape, and one aspect that plays a crucial role in ensuring the safety of networks is Ingress Timeout Stream ID. But what exactly makes it so important? Let’s delve deeper.
Ingress Timeout Stream ID helps prevent unauthorized access to a network by monitoring and managing incoming traffic streams. By assigning unique identifiers to each stream, it becomes easier to track and control data packets entering the network. This identification process acts as a gatekeeper, allowing only authorized streams while blocking suspicious or malicious ones.
By implementing Ingress Timeout Stream ID, organizations can fortify their network security defenses against various threats such as DDoS attacks, malware injections, and unauthorized access attempts. It adds an extra layer of protection by scrutinizing every incoming packet for authenticity and integrity.
Furthermore, this technology enables network administrators to set specific timeout durations for different types of incoming traffic streams. This ensures that if any stream exceeds its allocated time limit without proper authentication or authorization, it is automatically terminated – preventing potential security breaches.
Ingress Timeout Stream ID enhances network security by providing granular control over incoming traffic streams. Its ability to identify and terminate suspicious activities allows organizations to mitigate risks effectively and safeguard their valuable data from cyber threats. So whether you’re running a small business or managing a large enterprise-level network infrastructure, incorporating Ingress Timeout Stream ID into your security strategy should be considered essential
How does it work?
How does Ingress Timeout Stream ID work? Let’s dive into the details.
When data packets are sent over a network, they contain specific stream IDs that help identify and organize the flow of information. The Ingress Timeout Stream ID is a crucial component in this process as it helps manage and control the duration of incoming data streams.
Essentially, when a packet arrives at its destination, the system checks if it has an associated timeout value. If it does, the system sets a timer to monitor how long it takes for subsequent packets to arrive within that same stream. This ensures that all packets within a given stream are received within an acceptable timeframe.
If any packet fails to meet this timeline, exceeding the specified timeout value, it triggers an action such as dropping or re-routing the packet. This mechanism helps maintain network efficiency and security by preventing delays caused by stalled or incomplete data streams.
By effectively managing these timeouts and ensuring timely delivery of data packets, ingress timeout stream ID plays a vital role in maintaining smooth communication across networks while also safeguarding against potential security threats.
Ingress Timeout Stream ID works by setting timers on incoming packets to monitor their arrival time and take appropriate actions if any exceed predefined timeout values. It enables efficient network management while enhancing security measures in place.
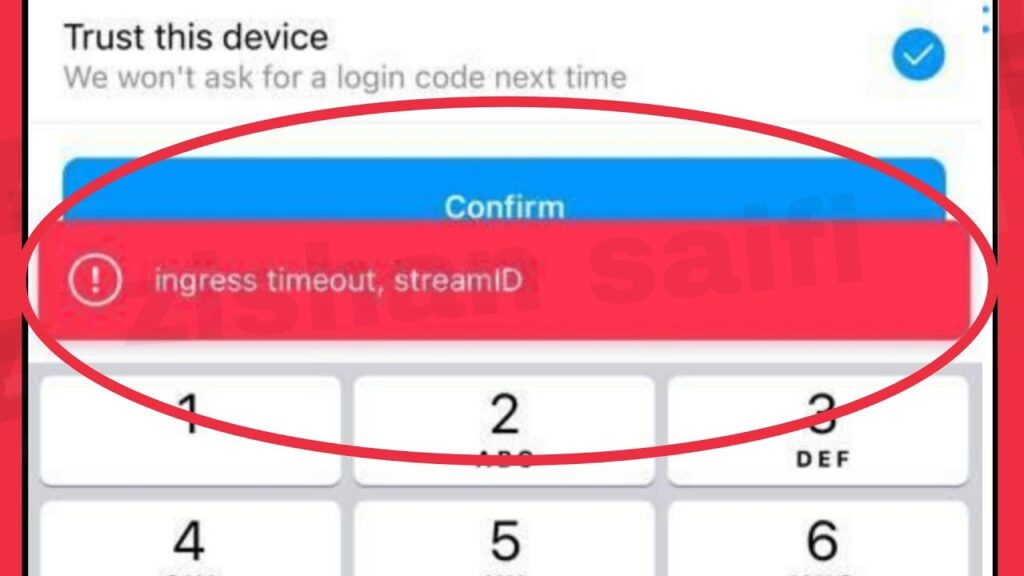
Common issues with Ingress Timeout Stream ID
Common issues with Ingress Timeout Stream ID
While Ingress Timeout Stream ID is an important tool for network security, there can be some common issues that users may encounter. One of the main problems is misconfiguration. If the timeout values are set too low, legitimate traffic may be mistakenly flagged as malicious and blocked. On the other hand, if the timeout values are set too high, it could result in excessive resource usage and potential vulnerability to attacks.
Another issue that can arise is compatibility problems with certain network devices or applications. Some devices may not support or properly handle the Ingress Timeout Stream ID feature, leading to inconsistent results or even malfunctioning of the network.
Additionally, troubleshooting and debugging can be challenging when dealing with Ingress Timeout Stream ID issues. It requires careful analysis of logs and packet captures to identify any errors or anomalies in how packets are being processed.
There might be performance concerns when implementing this feature on large-scale networks. The additional processing required by Ingress Timeout Stream ID could potentially impact overall network performance if not properly optimized.
To overcome these common issues, it is important to thoroughly test and validate configurations before deployment. Regular monitoring and auditing should also be conducted to ensure proper functionality and detect any potential issues early on.
In conclusion,
Understanding the common challenges associated with Ingress Timeout Stream ID implementation allows users to better optimize their network security measures while minimizing any negative impacts on performance or functionality.
Tips for optimizing Ingress Timeout Stream ID
Tips for optimizing Ingress Timeout Stream ID:
1. Set appropriate timeout values: It is crucial to configure the timeout values for Ingress Timeout Stream ID according to your network’s requirements. Setting too short of a timeout may result in false positives, while setting it too long can leave your network vulnerable to attacks. Find the balance that works best for your specific environment.
2. Regularly monitor and analyze logs: Keep an eye on the logs generated by Ingress Timeout Stream ID to identify any patterns or anomalies in network traffic. This will help you detect potential security breaches and take proactive measures before they escalate.
3. Fine-tune intrusion detection rules: Customize the intrusion detection rules based on your organization’s needs and threat landscape. Modify them as necessary to minimize false positives and ensure accurate identification of malicious activity.
4. Stay updated with patches and updates: Regularly update the software and firmware associated with Ingress Timeout Stream ID to benefit from bug fixes, performance improvements, and new security features provided by vendors.
5. Conduct regular vulnerability assessments: Perform periodic vulnerability assessments of your network infrastructure using reputable scanning tools or penetration testing services. This will help you identify any weaknesses or misconfigurations that could be exploited by attackers targeting your network.
6. Implement additional security layers: While Ingress Timeout Stream ID provides valuable protection against certain types of attacks, it should not be relied upon solely for securing your network infrastructure. Consider implementing other security solutions such as firewalls, antivirus software, VPNs, etc., to create multiple layers of defense against various threats.
Remember that optimizing Ingress Timeout Stream ID requires ongoing monitoring, fine-tuning, and adaptation based on evolving cyber threats within your organization’s unique context
Other tools and techniques for enhancing network security
Other Tools and Techniques for Enhancing Network Security
In addition to Ingress Timeout Stream ID, there are several other tools and techniques that can help enhance network security. One important tool is a firewall, which acts as a barrier between your internal network and the external world. Firewalls monitor incoming and outgoing traffic, allowing you to control access to your network.
Another effective technique is the use of virtual private networks (VPNs). VPNs create an encrypted tunnel between your device and the internet, ensuring that all data transmitted is secure and protected from prying eyes.
Network monitoring tools are also crucial for maintaining security. These tools allow you to continuously monitor your network for any suspicious activities or unauthorized access attempts. By detecting potential threats early on, you can take immediate action to prevent breaches.
Regularly updating software and firmware is another essential practice in enhancing network security. Software updates often include patches for known vulnerabilities, so keeping your systems up-to-date helps protect against potential attacks.
Implementing strong passwords and multi-factor authentication adds an extra layer of protection. Strong passwords should be unique, complex, and regularly changed. Multi-factor authentication requires users to verify their identity using multiple factors such as a password combined with a fingerprint or SMS code.
Conducting regular security audits helps identify any weaknesses or gaps in your network’s defenses. By periodically reviewing your security measures, you can stay ahead of emerging threats and ensure that your network remains secure.
Remember that while these tools and techniques are valuable in enhancing network security, it’s important to implement them alongside best practices such as user education about phishing attacks or social engineering tactics.
Stay proactive when it comes to securing your network!
Conclusion
Conclusion
Ingress Timeout Stream ID is a crucial aspect of network security that helps protect against potential threats and unauthorized access. By setting a specific time limit for incoming data streams, it ensures that only valid and authorized connections are allowed into the network.
Throughout this article, we have explored what Ingress Timeout Stream ID is, its importance in network security, how it works, common issues associated with it, and tips for optimizing its usage. We have also touched upon other tools and techniques that can be employed to enhance overall network security.
By implementing Ingress Timeout Stream ID effectively and addressing any issues promptly, organizations can significantly strengthen their defense against cyberattacks and safeguard their sensitive information. However, it is essential to remember that no single solution can provide complete protection. A multi-layered approach combining different security measures will yield better results.
As technology continues to advance at a rapid pace, so do the methods used by malicious actors to exploit vulnerabilities in networks. It is therefore imperative for businesses to stay informed about the latest trends in cybersecurity and consistently update their defenses accordingly.
In conclusion (oops!), understanding Ingress Timeout Stream ID’s role in network security empowers organizations to take proactive steps towards fortifying their systems against potential threats. With proper implementation and continuous monitoring of this key feature along with complementary security measures, businesses can create robust barriers against unauthorized access while ensuring seamless connectivity for legitimate users.
Remember: Network security should never be taken lightly! Stay vigilant, stay secure!